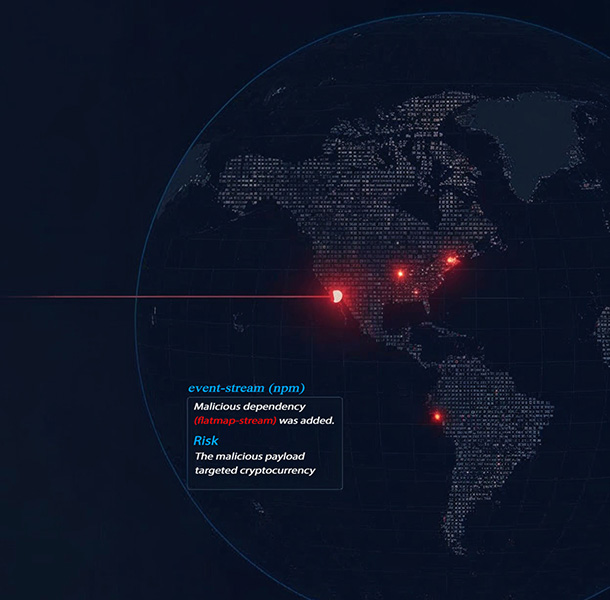
Continuous software dependency auditing with jurisdictional traceability
Identify foreign-hosted code and cloud dependencies, map provenance, and align with NIST SP 800-161 / CISA-SCRM—without heavy consulting.
Integrations with
What SecVektor does
Continuous assurance with evidence you can ship to auditors and leadership.
Dependency discovery
SBOM-style inventory across repos and pipelines with freshness tracking.
Jurisdictional mapping
Know where components and services are hosted, down to region-level signals.
Continuous auditing
Monitors repos, cloud, and CI/CD for drift; alerts on exposure changes.
Compliance mapping
Evidence mapped to NIST SP 800-161 / CISA-SCRM controls automatically.
Predictive risk scoring
AI-driven signals combine provenance, jurisdiction, and change velocity.
How it works
Fast onboarding, measurable outputs.
Connect repos/cloud
Link GitHub/GitLab and primary cloud accounts with least-privilege scopes.
Map dependencies & jurisdiction
We trace components, hosting regions, and software supply chain relationships automatically.
Get dashboards & artifacts
Dashboards, alerts, and compliance evidence ready for audits and leadership.
Use cases
Fintech / regulated
Meet examiner expectations with defensible software supply chain evidence: jurisdiction mapping, SBOM outputs, and drift alerts aligned to regulatory asks.

Health / sensitive data
Reduce jurisdictional risk around PHI/PII and vendor chains; surface foreign-hosted dependencies touching clinical and patient data flows.
Logistics / continuity
Prevent operational disruption from upstream component failures by mapping suppliers, hosting regions, and change velocity across critical lanes.


SaaS startups
Control dependency sprawl as teams scale: spotlight foreign-hosted packages, enforce jurisdictional guardrails, and keep CI/CD drift in check.
Compliance mapping
Built to operationalize NIST SP 800-161 / SP 800-53 + CISA-SCRM.
Controls mapped to evidence produced across code, cloud, and pipeline sources. NIST SP 800-161/53 provide federal supply chain and security baselines; CISA-SCRM focuses on supply chain risk management practices.
| Control | Evidence produced | Status |
|---|---|---|
| SR-5: Supply Chain Transparency | SBOM + jurisdiction map per repo | Passing |
| SR-10: Identity Management | Access review for integrations | In review |
| RA-5: Vulnerability Monitoring | Continuous drift + exposure alerts | Passing |
Differentiation vs. scanners
| Capability | SecVektor | Typical scanners |
|---|---|---|
| Provenance & jurisdiction | Yes — origin + hosting tracked | No — CVE focus |
| Foreign exposure alerts | Yes — code, cloud, vendors | Limited |
| Continuous evidence | Yes — audit-ready artifacts | Static reports |
| Pipeline coverage | CI/CD + supply-chain links | Mostly runtime |
| Governance posture | Access/identity context | Rare |
| Risk scoring | Provenance + jurisdiction + velocity | Severity-only |
| Deployment | No intrusive agents | Often agent-based |
| Drift detection | Continuous; retest built-in | Snapshot per scan |
Pricing
Annual plans with add-ons for deeper coverage.
Basic
Core repo discovery, jurisdiction flags, monthly reports.
Standard
Continuous alerts, compliance artifacts, prioritized guidance.
Premium
Advanced mappings, bespoke reporting, and auditor pairing.
Add-ons: modules, training, bundled compliance reviews.
FAQ
Is this a vulnerability scanner?
No. SecVektor maps provenance, jurisdiction, and governance; we integrate CVE data but focus on software supply chain assurance.
What data do you access?
Repository metadata, dependency manifests, and limited cloud descriptors with least-privilege scopes.
How do you handle privacy?
Encrypted in transit/at rest, no agents, and scoped access reviews with your team.
Does this replace compliance consulting?
We provide mapped evidence and reports; keep your consultant for policy/legal sign-off as needed.
How long to deploy?
Pilot onboarding takes 30–60 minutes; insights start populating within the first scan.